Making the Information Border Defensible
Why disinformation risk is now budgeted - and where Brinker.ai fits in
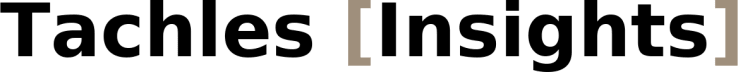
The WEF global risk survey has ranked misinformation/disinformation as the #1 short-term threat to economies and societies for the last two years. Regulators and security agencies now treat information attacks the way we treat cyber or physical intrusions -something you must monitor, detect, and mitigate. That shift is creating durable spend.
It’s never been cheaper to launch coordinated influence campaigns…until tomorrow. The barrier to entry is coming down, and modern AI makes fake content faster and more convincing. Governments and platforms are responding - Europe’s Digital Services Act compels very large platforms to reduce election-related information risks, and U.S. agencies like the FBI, CISA and ODNI regularly issue public warnings about foreign influence operations. Naturally, corporate boards expect preparedness, not excuses.
The simple idea behind Brinker.ai
Tachles VC portfolio company Brinker.ai is built for these most modern of challenges, acting as a “radar + response” platform for disinformation:
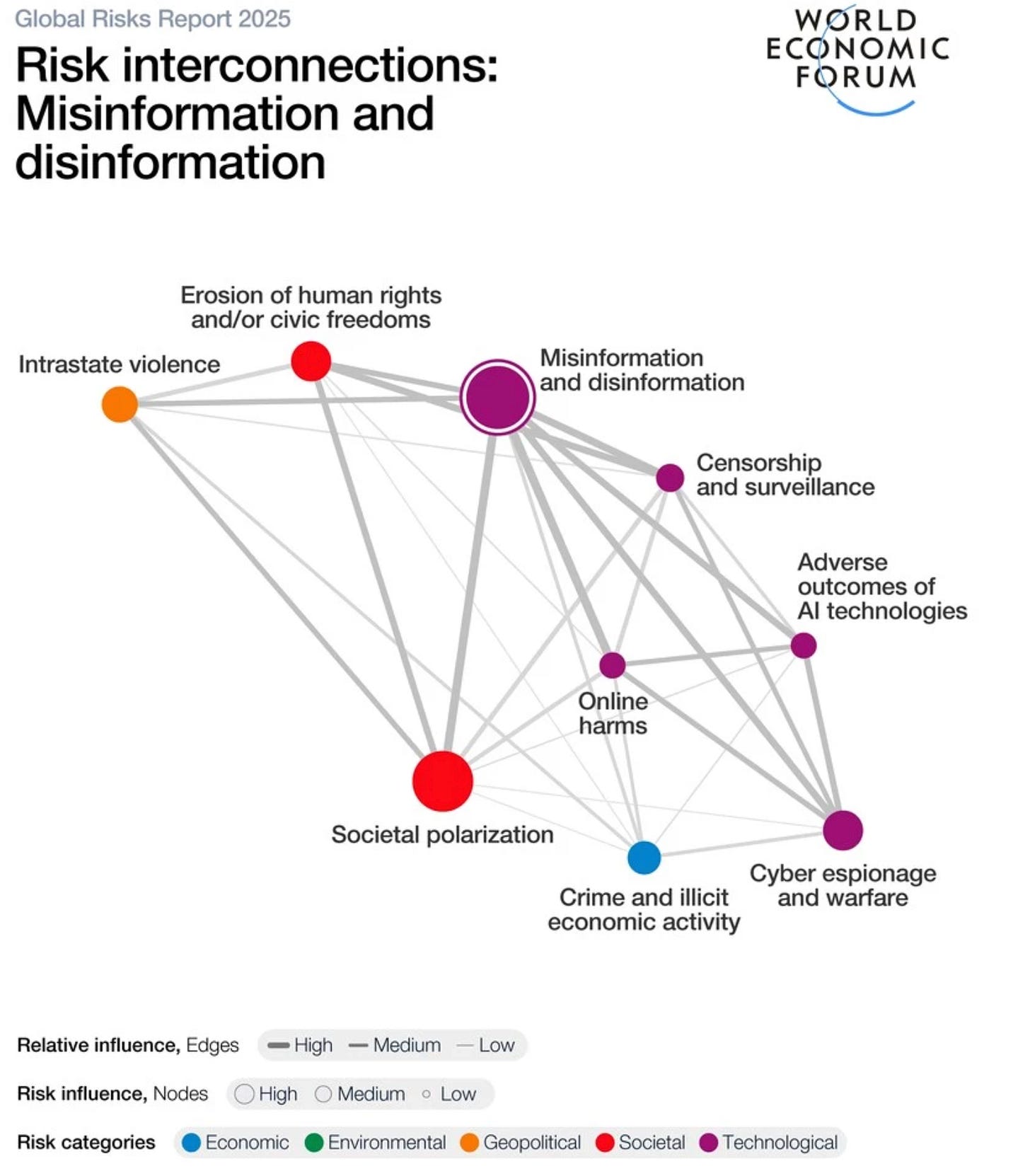
Find it early: AI detection and narrative intelligence to spot harmful storylines and coordinated campaigns across the open web
Understand it fast: Automated OSINT investigations map who’s pushing what, where it’s spreading, and potential impact
Act fast: One-click playbooks - from content removal and pre-legal actions, to counter-messaging - so teams can actually reduce reach and harm
Where it sells: public sector and major enterprises (brand, safety, elections, geopolitics)
For those working in the field, Brinker is listed on Splunkbase, and was named among “10 most promising defense tech startups of 2025.” Information-defense tooling is already becoming the norm at the upper echelons of both the public and private sectors - there’s a market here and it will only expand in the short and medium terms.
In practice: Countering mis- and disinformation
The scenario: A false story about your product’s safety is spreading across social media, and a coordinated smear of your company’s CEO starts trending. Newsrooms are calling and customer support is flooded.
After (with Brinker): Your team gets early alerts, sees the platforms being used, the users involved, and launches removal + response playbooks. The aim is simple: cut spread quickly and protect trust.
Chief Security/Intelligence officers, comms and brand safety teams, public-sector security and electoral bodies, and crisis-management firms - often the same stakeholders already managing cyber risk and incident response - need to be empowered.
The investment track
Pain that creates budgets. The combination of regulatory pressure, national security advisories, and corporate brand risk means organizations must mitigate information attacks - particularly around elections and major events. That makes Brinker’s “find → understand → act” stack a must-have, not a “nice-to-have.”
Clear product → clear value. Buyers can measure time-to-detection, time-to-takedown, and reduction in narrative reach. Those are concrete, stakeholder-friendly outcomes.
Ecosystem leverage. Presence on Splunkbase lowers friction with security teams; public ties to a blue-chip payments ecosystem like Mastercard add trust when procurement is strict.
Attractive software economics + multiple exit paths
Sticky subscriptions. Brinker’s “Disinformation radar + response” runs 24/7 like threat intel or brand protection. The product combines high-gross margins and natural expansion avenues - narrative threats are global, requiring elasticity at a global level across regions, brands, languages, and playbooks.
Industry precedent is on Brinker’s side:
Cyber/observability platforms buying analytics & detection: Cisco → Splunk ($28B, closed 2024)
External-threat/digital-risk vendors consolidating: ZeroFox taken private by Haveli Investments (2024)
Brand & social intelligence roll-ups: Cision → Brandwatch ($450M, 2021) and Meltwater take-private (2023), showing persistent buyer appetite for monitoring & narrative tooling
Payments and risk networks adding intelligence: Mastercard has repeatedly bought threat-intel assets (RiskRecon, CipherTrace) - a signal that large networks pay for outside-in visibility
Defense contractors as a buyer class:
BAE Systems is expanding software-driven cyber/EW and integrating acquisitions into its Digital Intelligence unit (Kirintec, 2024) to counter modern information-domain threats
General Dynamics (GDIT) is acquiring AI/ML and cyber firms (Iron EagleX, 2024) to bolster intelligence and information-ops missions - natural channels for Brinker-style capabilities
U.S. and allied strategies now formalize OSINT/information-space capabilities, aligning with Brinker’s find → attribute → mitigate workflow
The bottom line
Mission-critical use cases combined with active consolidation across cyber, threat-intel, brand intelligence, and defense, equal attractive exit optionality if Brinker keeps winning share.
Disinformation is now treated like any other enterprise and national-security risk - and budgets are following suit. Brinker.ai sells the software to spot campaigns early and shut them down fast, with credible ecosystem signals and obvious metrics buyers care about. The information space is the next defendable border - and a compelling place to make money.